Sharing documents might be an easy process in the modern digital workplace thanks to the multitude of file-sharing software options available on today’s market. However, file sharing securely is another matter altogether. The rapid pace of modern business can sometimes put enterprise professionals under pressure. Unfortunately, this can lead them to foregoing important security practices designed to safeguard their enterprises against data breaches and theft.
In this blog, we’ll run down the best practices for 2022 to help reinforce the vital steps that employees and their managers are advised to take to make sure that any file sharing they undertake never puts their company at risk.
Utilise VPNs
Employees can’t always be within the safe confines of an office, accessing enterprise files from their secure company network. Cybersecurity experts recommend employing a virtual private network, or VPN for short, for use in circumstances that require employing public wi-fi, for instance. Public Wi-Fi leaves firms vulnerable to hackers seeking to steal data but a VPN shields all web traffic inside a secure tunnel, hampering malicious actors’ efforts to intercept confidential files.
Employ strong passwords
Regardless of whether you are utilising a password manager or a specific solution that activates password protection on data files, it is always recommended that strong passwords are created. Robust passwords make it far more difficult for threat actors to obtain access to confidential data. Passwords should be between eight to 12 characters in length and employ a mix of letters, capitalisation, numbers and special characters when possible. The NCSC advises creating passwords by using three unrelated words to form the credentials.
Fix expiration dates for data files
When securely file sharing with customers and clients, companies often do not want specific files to be accessible forever. In such cases, setting accessibility expiration dates is a wise move. Shutting down access limits ensures that a file is forgotten about and helps companies account for all data in their care to appease regulators.
Regularly audit privileges of access
Admins should continuously review which individuals have access to which resources. Access should only be granted to employees or clients for as long as they require data to perform their role. The more frequently audits of access privileges occur, the tighter security will be.
Activate multi-factor authentication
No matter who is provided with access, organisations should use multi-factor authentication (MFA) configured to ensure that users are exactly who they state that they are. MFA can use two or sometimes more authorisation methods to ensure that a user’s identity is verified. MFA can be knowledge-based (information only a user knows), device based with PINS sent by text to smart phones or biometric data such as fingerprint, or voice recognition among others.
Educate and instruct employees to use secure file-sharing solutions
To make sure that it is always used correctly, staff must be efficiently trained on how to use the company’s secure file-sharing solution. As a result, it is a smart move to never select an overly complicated option. User-friendly solutions are available that can still deliver robust security.
Employ end-to-end encryption for data transfer
When it comes to secure file sharing, cybersecurity experts recommend peer-to-peer methods employing end-to-end encryption. Firms should always use direct file transfers in between users that are effectively encrypted on the transfer’s sending end and efficiently decrypted on the receiving end. The result is that data remains safe while it is in transit and protected from any attempted unauthorised access or manipulation.
However, the encryption algorithm employed is a crucial part of this process. Companies must use a powerful encryption specification like the Advanced Encryption Standard (AES), a global standard for maintaining safe online communications safe. Encryption software in the UK should always be approved by the NCSC and combine multiple layers of protection to ensure it is difficult for cybercriminals to crack.
Reviewing data files before they are shared
Finally, you might be sharing a data file with an individual outside or inside of your organisation, but either way, it is a smart move to review any content involved before data is sent. To avoid inadvertently sending an incorrect or irrelevant document, or even inappropriate material to the recipient, a review of data is wise.
Secure file transfers simplified with Galaxkey
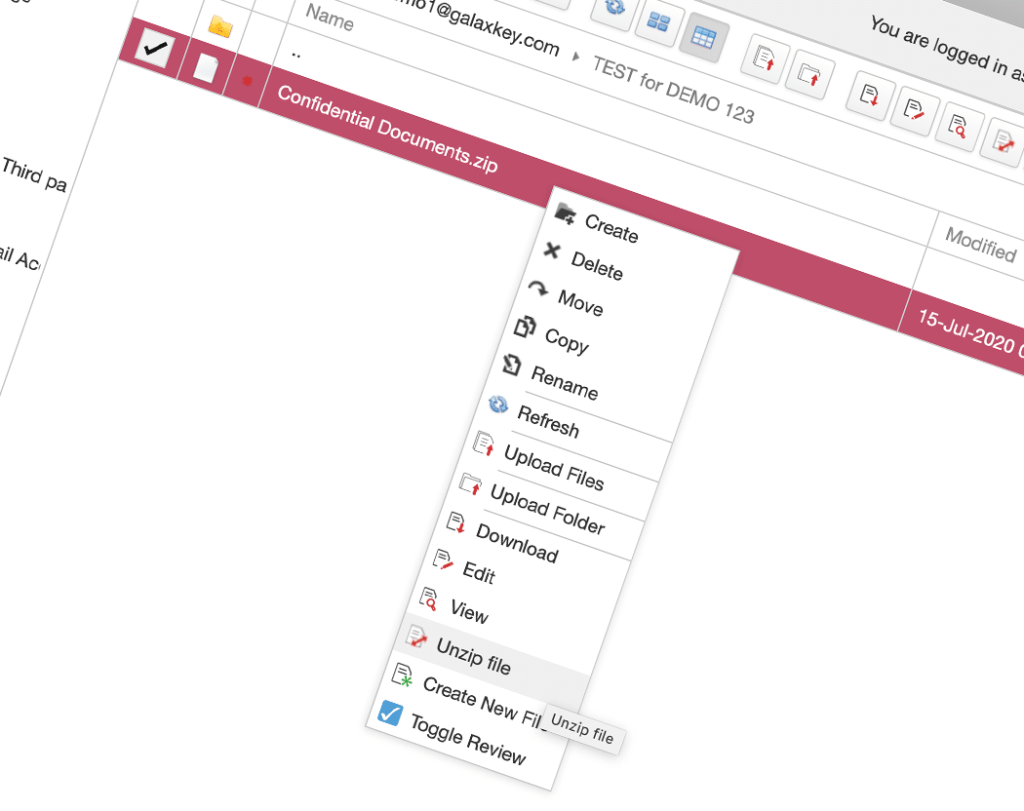
At Galaxkey, we have developed a cutting-edge solution for secure file-sharing with advanced protective features. Files can be secured on a wide range of operating systems, including Mac and Windows and no limits are ever placed on files size. Files can be protected in cloud storage with secure vaults supported. Designed to be exceptionally user-friendly, employees can encrypt data files before transfer with a single mouse click, adding three powerful levels of protection to any information shared.
To start using Galaxkey’s secure file sharing solution, access your free 14-day trial today.