The digital transformation has caused cybercriminals to launch yet more attacks on organisations. They’re targeting employees who connect on unprotected personal devices and networks, which is why it’s critical for companies to have advanced security measures in place.
There are many threats in the digital world and some of the most dangerous for companies are data breaches. Criminals have more opportunities to exploit businesses and steal sensitive data, which can lead to losing customer trust, large sums of money being stolen, and other consequences.
For this reason, various cybersecurity measures, such as Virtual Private Networks (VPNs) and data protection services, exist.
We asked Randhir Shinde, the CEO of Galaxkey, to share his views on the current digital environment, cybersecurity threats, and their prevention methods:
How did the idea of Galaxkey come to life? What has the journey been like since your launch?
We founded Galaxkey in 2010 to provide a data protection solution that is highly secure and easy to use.
It’s the perfect balance between privacy protection, ease of use and flexibility. And it’s much needed to protect data against cyber thieves.
Our mission is to provide the highest level of security for our users in a very simple and easy way. We want them to rest easy that their data is safe and protected.
We also work constantly to improve our products and services, so that we can offer the best possible protection for our users.
Cybersecurity moves fast. It has to, as it needs to stay ahead of the many new threats that appear on an almost daily basis. Because of that, it’s an interesting space to be in. So interesting in fact, that Sir George Zambellas joined us as our Chair in 2016. He sees what value our company can add towards making things better and wants to help us achieve even greater things.
Can you tell us a little bit about what you do? What methods do you use to protect data?
We take data security very seriously.
We have several products and each one uses the same identity-based encryption model. It means that each time someone wants to access a piece of your data, they must present the correct identity and authorization. If they don’t, then they cannot retrieve the data.
By tying access to identity, it allows users to work from many devices, platforms, and regions with no loss of security. And it also frees an organization to work how it wants to while remaining protected at all times.
We secure data with FIPS 140-2 compliant encryption algorithms, which is a benchmark standard set by the US Government.
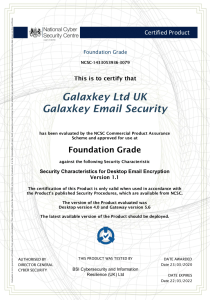
By combining this with identity-based authentication, we are amongst the most powerful data protection platforms available today. In fact, the NCSC has tested and approved our encryption to CPA standards.
In your opinion, which industries should be especially concerned with encrypting their data?
To start, this isn’t just about encrypting data.
It’s about protecting your most valuable asset from harm, no matter where it is or where it goes. It’s something that every business in every industry needs to do, and it’s no longer a “nice to have” – it’s a necessity.
Yes, there are industries that hold incredibly sensitive data, and these are heavily regulated. Finance, education, and the public sector, for example, need an extremely high level of protection. Not only to ensure the safety of the data that they hold but also to ensure that they meet the stringent regulations they are guided by.
Yet, EVERY business holds data that needs protecting. I can’t think of one industry that doesn’t hold sensitive data of some description.
Think about all of the PII (personally identifiable information) that every company holds – names, addresses, bank details, tax numbers… The list is endless. If this information were lost to a threat, then it could mean disaster for the business and for the individual whose data was lost.
Do you think the recent global events affected the way people perceive cybersecurity?
Covid-19 forced businesses and their people to take a long hard look at how they secure their data.
There was much talk of the “new normal”, with a mass exodus from traditional offices to working from home. The challenges that this brought to businesses were immense.
They needed to ensure the safety of their data, so cybersecurity products were pushed to the forefront of everyone’s minds.
It looks as though home working is here to stay, too, so businesses will need to continue to mobilize. They’ll need to be flexible in how they approach securing their data.
There is no more flex to “wait and see” – if you have data, you need to make sure it’s safe.
What issues have you noticed arise most often among teams working remotely?
Remote working brings with it a whole array of cyber challenges, and one of the biggest challenges brought on by the “new normal” is that many employees need to use their personal devices and their home network for work.
This gave hackers a much greater opportunity to steal sensitive information due to limited security on both the devices and the networks.
It’s an issue that Galaxkey has been able to resolve for our users very easily, though. They can access our platform on any device and any network. It allows them to store and send important data incredibly safely.
In your opinion, what are the biggest mistakes companies make when it comes to handling large amounts of data?
Complacency is one of the biggest mistakes many companies make when it comes to handling data.
The reasoning that it won’t happen to them or that they have nothing to protect is often used as justification for not taking data security and privacy seriously.
However, the truth is that companies of all sizes are equally at risk when it comes to data breaches. All data is precious and we need to treat it as such. Lost trust or a leak of data can be catastrophic, both for the data owner and the company entrusted to keep it safe.
Another mistake is that focus has traditionally been to stop hackers from accessing your business, not about protecting the data if – and when – defences are breached. Organizations need to see the necessity of focusing on data protection in the event of a breach.
Finally, I believe that it’s a mistake to trust third parties and cloud provider systems without fully understanding how this data is kept safe, where it is kept, and what happens to it when it is transmitted from A to B.
Every organization needs to be fully aware of these basics at every step of the journey of their data. If they don’t, it could lead to serious consequences.
What would you consider the most serious cyberthreats prominent today?
Cyberthreats are becoming more complex and harder to deal with.
They range from ransomware attacks, where data is held hostage against a demand for payment, to national-level threats, denial of services, and specific targeting of areas that are critical to national infrastructure and defence mechanisms.
The increasing interconnectivity of our digital worlds means that data is ever more valuable to attackers, so it’s more important than ever to have the right mechanisms in place to protect it. And that means having protection in place even if the attackers manage to get through your outer defences.
Talking about average Internet users, what security measures do you think everyone should implement to protect their data?
Everyone needs to understand that they can be hacked – that no one is off-limits.
Data is the new gold for criminals, and the theft of it can have devastating effects on individuals and businesses.
If we can educate people about the dangers of cyber crimes and how simple security techniques can protect them, then we’ll start getting somewhere.
Everyone has a lock on the doors to their house so that they can make the contents safe from theft, and in the same sense, everyone needs to have a lock on their sensitive data so that they can keep that safe from theft too.
The simplest way to do that is to encrypt the data.
Easy-to-use encryption for your enterprise.
At Galaxkey we have created a state-of-the-art platform that can encrypt your data and keep it protected from any threats. Whether you want a demonstration of how to use our platform or a FREE 14-day joyride then click on the link below to get started.