Multifactor authentication (MFA) is a recommended method for safeguarding secure information protected by passwords. MFA adds an extra layer of protection that can mitigate date leaks and breaches by, making it more difficult for an intruder to access areas requiring credentials to enter.
Even if a threat operator manages to obtain the username and password of a user, MFA can foil their attempts by demanding further information before access is granted. In this blog, we’ll look at the three categories MFA can be broken down into.
1. Something you know
Knowledge-based authentication (KBA) is the first type of MFA and involves information that only the user knows. This may be a PIN, a second password, or simply the answer to a specific security question. This last method sees a question and static answer established when a user creates an account. This option is also used often for account recovery by verifying a user’s identity when they can’t remember their password.
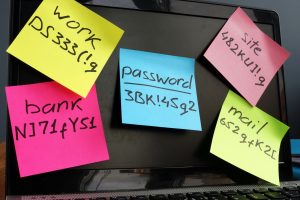
The drawback of this option is if a user employs common knowledge as the answer to their question, or for a PIN or password, an attacker can guess or look this information up on social media. Many people leave their accounts vulnerable by basing passwords around the names of their children, pets or favourite football team.
2. Something you have
Another form of MFA involves something a user has. For a digital account, this usually involves a token that instantly generates a single-use password. There are three different types of token authentication commonly being used.
SMS token authentication involves an organisation issuing a PIN to a user by text. Upon receipt, the user inputs the PIN as a single-use password to access their account. Unless the attacker has access to their victim’s mobile phone, they will not be able to bypass security. Similarly, email token authentication sends the PIN to a user’s email account address, although unless the account has MFA established, it can be at risk.
Finally, software token authentication insists that the user verifies their identity through an app on a tablet or smartphone. When prompted for a single-use password, the user opens the application, and is given a time-restricted PIN they must enter. In most cases, these applications generate a brand-new PIN every minute to foil hackers trying to retrieve SMS token information.
3. Something you are
The last type of MFA uses biometric data. Users are prompted to scan their fingerprint, retina, or face to access their account or technology. Biometric information must be scanned and entered in advance so that it can recognise the user each time they attempt access. Commonly used by Apple technology, this method of MFA is exceptionally flexible as users do not need a personal device present to pick up a code. It also uses unique data for MFA, that is not easy for hackers to replicate. Companies adopting biometric MFA should remember that this type of data is considered personally identifiable information (PII) and must be protected appropriately against potential breaches.
For next-generation encryption and electronic signatures to enhance the data protection and security access protocols you use, contact Galaxkey today for a free trial.