Malware unleashed on today’s enterprises takes many forms. As a result, there is often a great deal of confusion regarding what these insidious programs are designed to do and what level of harm they can cause. In this blog, we’ll take an in-depth look at three different attack types that your firm must be aware of. Read on to explore computer viruses, worms and trojans in greater detail and see how they differ from one another.
What is a computer virus?
A computer virus is a malware that, once executed, will self-replicate by altering other computer programs and injecting its own malicious code. If this replication succeeds, the impacted areas are infected.
Insidious virus writers employ social engineering or exploit critical vulnerabilities to infect computer systems with the aim of spreading the virus.
The purposes of viruses are varied. They may be designed to make profits for threat actors, demonstrate vulnerabilities, sabotage or deny access to systems or service to legitimate users. Viruses can cost companies billions by causing total system failure, corrupting data, wasting resources, raising maintenance costs, stealing personal information and logging keystrokes.
What is a worm?
In computing, a worm is a type of self-replicating malware program. Its prime objective is to infect other devices by continually duplicating while remaining active on the systems it infects.
In many cases, worms utilise computer networks to disseminate, relying on security failures or vulnerabilities on the target device to obtain access. Computer worms nearly always inflict some level of harm to the network they attack. At the very least, they will consume bandwidth. Worms differ from viruses in the way that they do not require a user to execute them as they are self-replicating.
Another difference is that many worms are engineered to just spread rather than change the systems that they pass through. However, even a payload-free worm can cause substantial disruption by increasing the volume of network traffic.
What is a trojan?
Sometimes called a trojan horse, the term trojan refers to any type of malware that intentionally misleads users regarding its purpose by impersonating a legitimate computer program. This form of malware gets its name from the Ancient Greek tale of the deceptive wooden horse that resulted in the fall of Troy.
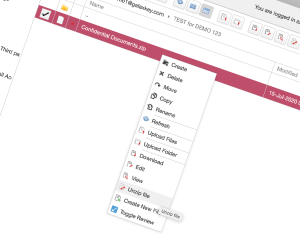
The most common way that trojans are spread is via social engineering attacks like phishing. For instance, a user might be fooled into executing a dedicated email attachment that is disguised to appear like a simple document such as an Excel spreadsheet. After the executable file has been opened, the malicious trojan is installed on their device.
A trojan can carry all kinds of payload, but most are used to create a backdoor that gives attackers unauthorised access to an infected device. Trojans often enable access to personal data like internet activity, passwords, banking login credentials and other forms of personally identifiable information (PII). Unlike worms and viruses, trojans rarely replicate themselves or inject malicious code into other data files.
For enhanced cybersecurity for your firm, contact Galaxkey today to access a free 14-day trial of our secure workspace equipped with three-layer data encryption.