The term file integrity monitoring, or FIM for short, refers to a specific IT security technology and process developed to test and check application, data base and operating system software files to assess if they have been tampered with or corrupted. FIM is a form of change auditing and validates and verifies files by comparing the most recent versions of them to a trusted and known “baseline.” Should FIM software detect that data files have been updated, compromised or altered, it will generate alerts to guarantee further investigation, and should it be necessary, for remediation to take place. FIM encompasses forensic or reactive auditing but also active, rules-based proactive monitoring.
What makes File Integrity Monitoring vital?
FIM software scans, analyses and reports on any unexpected alterations to important files within an IT environment. As a result, it provides an essential layer of application, data and file security, but also aids in accelerating the speed of incident response. Below are the four main roles of FIM.
Detection of illicit activities
If a threat operator penetrates an IT environment, the firm must determine if the attackers have tried to change any critical operating system or application files. Even when log files are altered or avoided, FIM can detect changes to core elements of an IT ecosystem. Through FIM, firms can protect and monitor the security of their data, files, applications, and operating systems.
Pinpoint any unintended alterations
File changes are sometimes made mistakenly by employees. While this is often harmless, at other times such errors can result in security backdoors, or dysfunction to business continuity or operations. FIM simplifies auditing by helping firms zero in on inadvertent changes so remediation can be made.
Monitoring system health and verifying update status
Firms can check if data files have been patched with the latest version by simply scanning installed editions across multiple machines and locations using the FIM’s post-patch checksum.
Keeping compliant
FIM software’s capability to audit changes and monitor and then report on specific types of activity is necessary for a wide range of regulatory mandates.
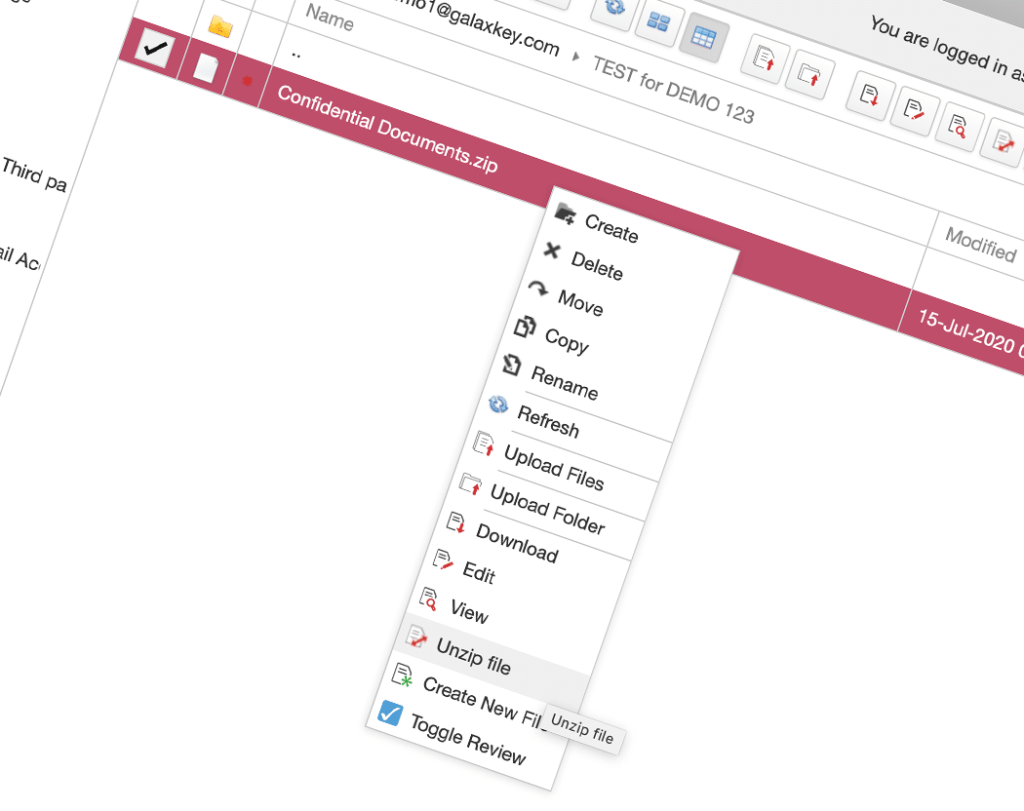
At Galaxkey, our system streamlines security processes, empowering enterprises to keep data records and files safe. Boasting three-layer encryption, you can make sure the data you send and store always matches your set baselines. If changes take place during transfer of data, alerts are generated informing recipients that files have been interfered with. Contact us today to access a free 14-day trial of our system and secure your files against threats.