Ransomware has become an increasingly popular form of attack for threat operators in recent years. So much so that many cybercriminal gangs have switched out credential stealing, data theft and other forms of attack and transformed into ransomware operations for the lucrative rewards they can offer.
Ransomware groups aim their attacks at a wide range of victims in multiple sectors. There are no fixed parameters on the size an organisation must be to qualify as a target, nor a specific sector in which they need to operate. Enterprises, educational institutions, and local government are all potential prey for ransomware gangs, and operations ranging from small businesses to multinational corporations have experienced attacks.
In this blog, we’ll take an in-depth look at ransomware and how organisations can protect themselves against it. Read on to find out more.
What is ransomware?
Essentially, ransomware is a type of malicious software. Sometimes referred to as crypto malware, ransomware is designed to infect company networks and devices and lock owners and admins out of the essential system and data they need in order to function. Data and operating systems are encrypted, ensuring that users must have a specific decryption key to access the information they use and the solutions necessary to access them.
How is ransomware deployed?
Company devices and networks can be infected by ransomware attacks through multiple channels. Operating systems and applications that are not updated can create vulnerabilities for ransomware operators to exploit, as can the use of public Wi-Fi. While insufficient security practices are a common cause of ransomware attacks, perhaps the most popular attack vector used is phishing emails.
Emails may include malicious links with seemingly legitimate attachments that require downloading. However, if users are hoodwinked into clicking on these downloads, malware payloads are deployed and start to run on machines. While in some cases the payload may be ransomware, in others it will be a solution designed to deliver the attacker persistent access so they can assess whether systems and files are worth encrypting.
When ransomware operators are playing a longer game, these emails may include direct links that take users to a bogus website masquerading as a legitimate login page for a trusted site. In some cases, when the recipient interacts with the page, it will trigger a malware or ransomware download. However, the page may just harvest their password and username. These credentials may be used by the gang to penetrate the company’s systems and evaluate the victim’s data and systems before infecting them.
How does a ransomware attack work?
After the attackers have identified important systems and data, they will use ransomware to encrypt them and leave a text note or landing page explaining what has happened. Typical notes state that the user is a victim of a ransomware attack, list the ransom amount that must be paid for the decryption, and provide with payment details and terms. As it is notoriously difficult to trace or recall, ransomware operators usually demand payment in cryptocurrency.
Operators may threaten victims, stating that they will destroy their data, but if a firm has kept up-to-date backups, they can refuse to pay and return to normal operations. To counter this, ransomware gangs have developed a strategy called double extortion. When they first infiltrate a business’s systems, attackers steal private data files before encrypting them. They hold the stolen data hostage and use it as leverage against a refusal to pay.
If a payment is not forthcoming, the ransomware gang will threaten to expose the private data online. Typical files stolen include records on customers and staff that include personally identifiable information (PII), and sensitive company and client data that often includes financial details. Operators will usually post a sample of stolen data on their dedicated leak sites to add pressure and as proof of the attack, but may also list it on “dark web” forums in the form of an auction with files to be sold to the highest bidder.
What are the consequences of a ransomware attack?
Ransomware attacks can disrupt business processes, stopping operations entirely in some cases until data and systems are released. The impact of an attack almost always involves a data breach, which can be costly for companies. Fines from regulators, compensating data subjects, forensic investigations, remediation, and technical solutions all add up and long-term costs can involve falling stock prices and loss of reputation and business.
How can you stop ransomware attacks?
Once an attack has been unleashed, you cannot stop ransomware, but the answer is prevention. There are multiple measures that you can put in place to protect your firm that can avoid or repel an attack, but also mitigate damage if one gets past your defences.
Ensure that your endpoint security is strong and that you use antivirus and antimalware software Along with your operating systems and software, all cybersecurity solutions must be kept up to date with the latest patches available.
Make sure that your staff are aware of the risk of a potential ransomware attack and how to spot and deal with the phishing emails that deploy them. Remember that keeping a regimented system of backups is essential to remaining resilient when attacked, and will help you restore your business to normal operations swiftly.
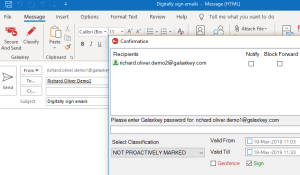
Use powerful passwords to protect your systems and accounts, backed up by multifactor authentication and use data encryption software to protect the information that you store on servers and in user email accounts.
A comprehensive security solution for your firm
At Galaxkey, our secure system has been designed to protect enterprises, local authorities, colleges, and universities against attacks. Our system stores no passwords and has zero backdoors that can be exploited by ransomware operators. We also provide powerful three-layer encryption that allows you to keep your confidential data safe from intruders on your system, and has been approved by the National Cyber Security Centre.
For more information and to arrange a free two-week trial, get in touch with our technical team today.