From enterprises and educational institutions to governmental departments and healthcare organisations, all operators require a way to transfer data files securely. Legislation like the General Data Protection Regulation (GDPR) demands that care and attention is taken when private information belonging to data subjects is shared, sent, or stored. Steep fines are dealt out to companies and local authorities alike that fail to take sufficient measures to safeguard the data they handle.
To remain competitive, firms of all sizes are advised to keep company information confidential. From financial agreements to trade deals, enterprises in every sector have a need to keep their activities private until they are ready to make them public.
While once cybercriminals sought to simply steal funds from their victims, these concerns have led many to seek out private and confidential data in their attacks instead. Targeting companies with poor security measures and negligent attitudes towards data protection, threat operators use a variety of tactics to seize data files. As a result, it has never been more important for all operations where data is transferred to take appropriate steps to protect it.
In this blog, we’ll take an in-depth look at the most secure method of file transfer and explore its many benefits. Read on to find out more.
Using encryption software
Many enterprises and organisations have secure areas on their network where the most sensitive data files are stored. Unfortunately, when firms need to share information with entities outside of their organisation, this requires giving third-parties access to areas of your system.
Additionally, while data files may be safe on a company’s dedicated network, if they transfer the information to another location outside of the system, they instantly lose this protection. For example, a file might be transferred to a pluggable device like a USB drive or uploaded to an online storage solution like Dropbox. Files might also be shared as an attachment via email, but the same rule applies, and the data is put at risk.
Encryption software was designed to protect the data file itself, rather than creating a secure area. The key advantage of this is flexibility with security. Data files can be moved, transmitted and shared without ever being compromised.
Effectively scrambling data files to appear as meaningless lines of random characters, encryption renders all information entirely indecipherable. Unless the viewer has been issued with the correct decryption key, they will not be able to read the contents of a file. Users who wish to transfer files securely to an individual can issue them with a key, ensuring that only they will have access.
As a result, companies can benefit from premium levels of data security. If a file is attached to an email and sent to the wrong address, or data is uploaded to a USB drive or laptop that is later lost, no data breach will occur as long as encryption was deployed.
Employing encryption also offers complete traceability. It offers businesses a complete record of every user who interacts with a data file and any amendments made. Being able to show data regulators the complete history and journey of a data file can be extremely useful to prove that sufficient security measures are being adopted and that a company is compliant.
Share and store your company content securely with Galaxkey
If your organisation is committed to data security and is now seeking a solution that can keep private information free from snoopers, at Galaxkey, we can help. Our secure system has been designed to deliver a user-friendly way for you to safeguard your files whether they are being uploaded to cloud storage or sent via email. Whether data is at rest or on the move, our state-of-the-art system can ensure it is only viewed by those with appropriate authorisation.
Instead of protecting files within a fixed location within the boundaries of your operation, we use powerful three-layer encryption to safeguard the data itself. As a result, your business processes are never hampered, with data files free to move beyond your security defences while remaining protected from prying eyes.
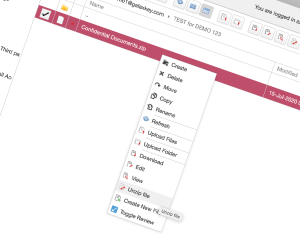
Based on the onion model recommended by the US Government, our robust encryption has been approved by the UK’s National Cyber Security Centre (NCSC). Exceptionally simple to use, encryption can be added by Control-clicking on a Mac or right-clicking on a PC. Once a user has enabled our Personal Vault Encryption, a data file can be emailed or uploaded to cloud storage options like OneDrive, Google Drive, iCloud, and Dropbox, with no limitation of size and only those with permission can view the contents.
If you are ready to upgrade your data transfer protocols with second-to-none security, get in touch with our technical team today to enjoy a free 14-day trial.