Privacy in Data: War shows the weaknesses – Admiral Sir George Zambellas
Privacy in Data: War shows the weaknesses.
The conflict in the Middle East, following the strikes by the United States and Israel on Iran, marks yet another major geopolitical moment.
But, unseen amid the obsessive imagery of explosions, drones, jets and general military hardware, is the biggest battle of all: the data battle – more strategically important than any conventional land, sea, air, or space power. Data is the enabling precursor to all military-strategic effectiveness because it is the lifeblood of them all.
During many years of service, including my time as First Sea Lord leading the Royal Navy, I saw the obsessive nature of military platform counting. Of every sort. And understandably so: it is an obvious measure of capability. Scale counts. If governments wilfully degrade capability through strategic underinvestment and procurement self-harm, as the UK has, then don’t whinge when you’ve too few assets to deploy.
But, bigger still is the failure to invest in data sovereignty – the assured privacy of critical national data. Don’t rely on others, including the United States, to keep your data safe. It is a national responsibility, widely recognised by certain nations globally – nations that evolved through a dependency on US global software, but now realise (sometimes too late) that their own paramount data sovereignty is compromised, and their data back door is wide open to exploitation in networks, communications systems, energy grids, logistics and digital infrastructure. And in the military.
Those who protect information and understand it better than their adversaries, hold a decisive advantage. Some CEOs do. Most do not. Few military leaders do. Almost no UK politicians do (less than 10% have any significant form of STEM education, while in China it is greater than 30%). This is the ability to understand the data detail sufficiently to make selective judgements. One level down, courageous CTOs and CIOs who are willing to tell their Boards the truth, are in short supply in most enterprises.
The Silent Battlefield in Cyberspace
Before, during and after physical conflict begins, activity in cyberspace intensifies. But the data privacy battle has begun decades earlier – or it should have. Government systems, energy providers, telecommunications networks, financial institutions, and transport systems are attractive targets. These are not peripheral assets, or disconnected. They are critical to national stability and societal confidence.
For an adversary, offensive cyber operations are comparatively low cost and high impact. They are often difficult to attribute and can be highly disruptive. Most importantly, they frequently succeed, not because technology has failed, but because people have. And, usually, that means leadership.
In the vast majority of breaches, vulnerability arises through poor design, and when – under pressure – data is transmitted, shared, or accessed. Human error, legacy processes, weak leadership, and misplaced trust are often the entry points. Mostly, they are failures of governance, oversight, or data control.
In war, as we are witnessing, such risks are horribly exposed.
The Reality of Data Privacy
In many boardrooms, the phrase data privacy, or sovereignty – choose your noun – is used confidently. In practice, it is often misunderstood.
Storing data in a particular location does not in itself guarantee sovereignty. Nor does using an encrypted cloud service automatically mean that control remains with an organisation.
If encryption keys are held outside your jurisdiction, ultimate authority over access may not rest with you.
Legislation such as the CLOUD Act illustrates how governments can lawfully compel access to data held by service providers under their authority, even when that data is stored elsewhere. This is not a political observation. It is simply a legal and structural reality.
True sovereignty means genuine control over encryption keys, infrastructure and governance. It means the ability to determine who can access sensitive communications and critical operational data without reliance on external custodianship. Resilience extends beyond perimeter security. It must reach the data itself.
Control Rather Than Convenience
Over the last decade, convenience and efficiency have shaped much of digital transformation. Cloud services have delivered flexibility and scale. They have enabled organisations to innovate quickly and operate globally.
However, geopolitical threat does not reward such conveniences.
Resilience requires thoughtful architecture. It requires clarity about where data resides, who controls the keys and how systems would function if external connectivity were disrupted.
Federated data protection models governed within sovereign jurisdiction and designed to operate independently, if necessary, are no longer theoretical discussions. They are part of responsible strategic planning.
Leadership Responsibility
In military doctrine, information superiority has always been decisive. It is central to decision-making, operational choice, and tempo.
Today, data is not simply an IT matter. It is a strategic national asset.
As the war in the Middle East evolves, none of us can predict precisely how events will unfold. But we can control our preparedness.
Leaders in government and industry should be asking clear and candid questions. Do we genuinely control our data? Who holds our encryption keys? Could external legal frameworks override our assumptions? Could we operate securely if global cloud services were unavailable? If, indeed, they understand these questions, they must be asked by governments,CEOs and generals today. But, regrettably for some, they should have been asked many, many years ago.
Preparedness in uncertain times is not a sign of fear. It is a mark of honest, responsible leadership. And it is never too late to do better.
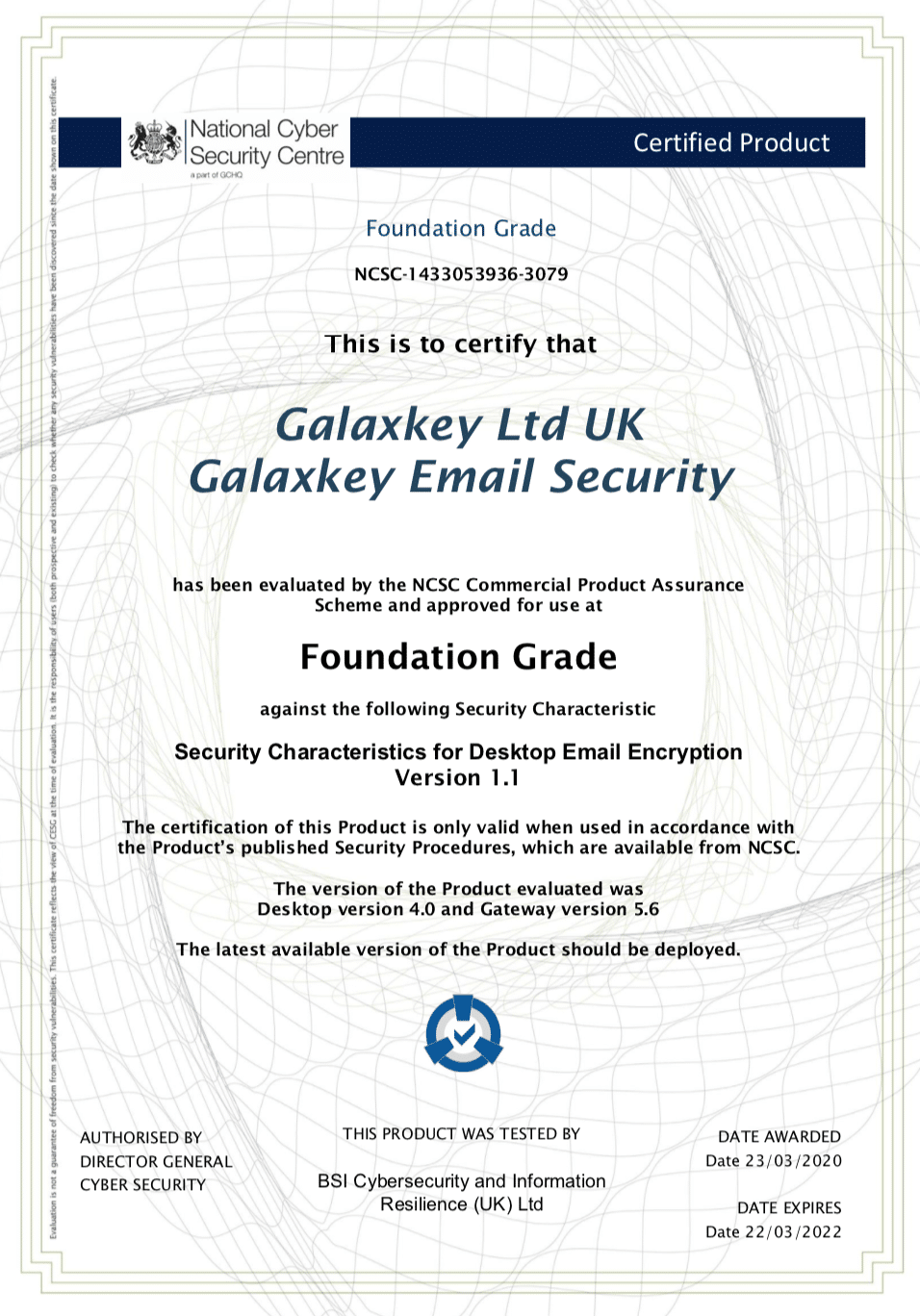
Admiral Sir George Zambellas is the Group Chairman of Galaxkey Group – A specialist in data security company.