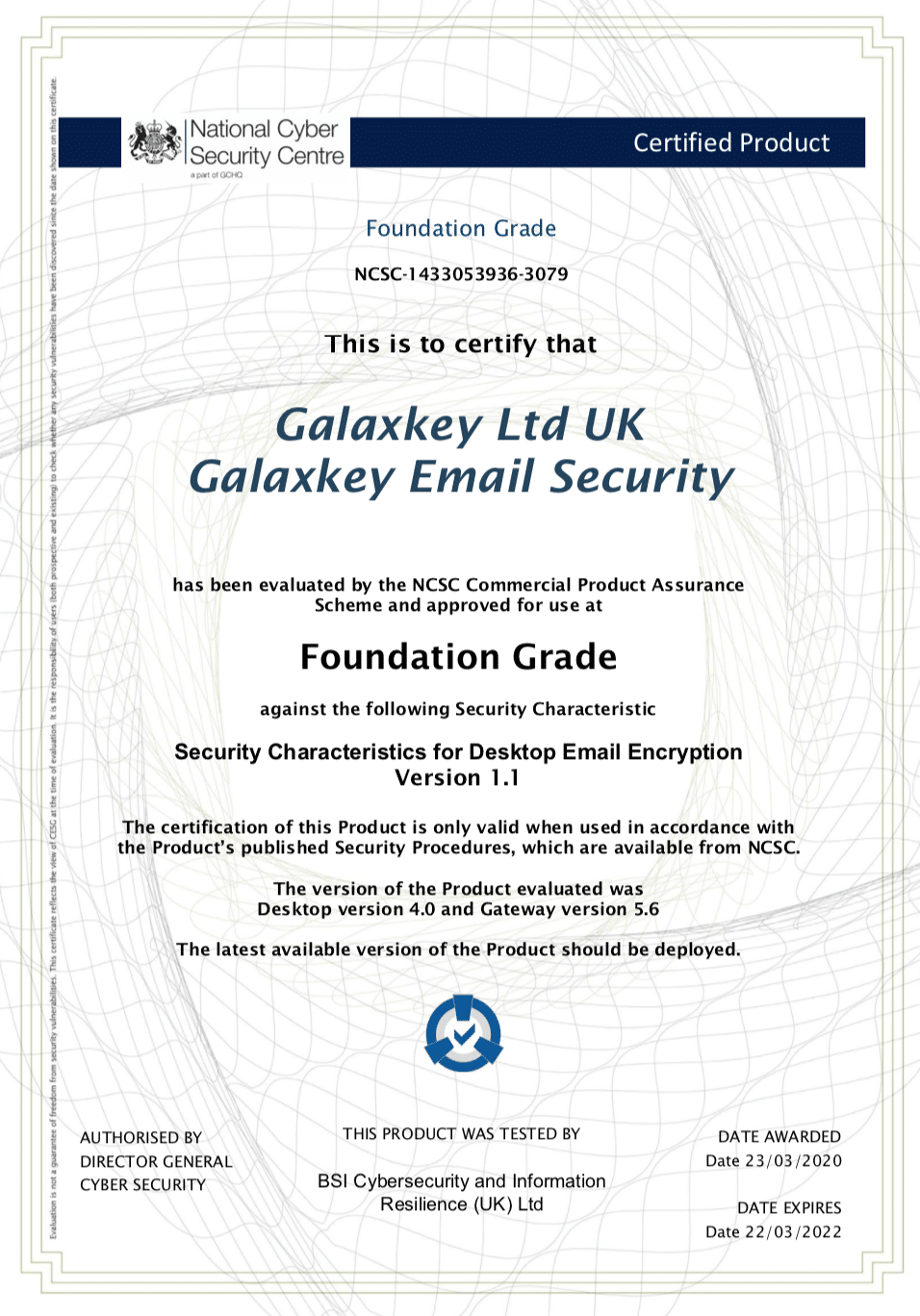
Galaxkey is very proud to announce that we have achieved certified CPA compliance from the National Cyber Security Centre. This comes after exhaustive testing of our email encryption platform and our internal security operations.
What is the National Cyber Security Centre?
The National Cyber Security Centre (NCSC) is a part of the Government Communications Headquarters, commonly known as GCHQ. It’s the organisation responsible for providing intelligence and information assurance to the UK government.
The road to certification
The road to certification has been long and intense, and we are incredibly proud of our development team for their great commitment to Galaxkey in attaining this highly prestigious certification.
So what does this mean?
Galaxkey users can have confidence in our technology because our encryption methodology has been proven to provide best in class security, and our GXK file architecture has proven to be impenetrable to external threats.
Of course, we always knew this, but it’s nice to get it validated!
Now with OFFICIAL and OFFICIAL SENSITIVE status, corporations and Government departments can share sensitive data with complete confidence in our platform.
After all, we have the UK Government seal of approval.
Find out how Galaxkey can secure your organisations data by visiting our website or get in touch directly at sales@galaxkey.com



